The rise of authorised push payment (APP) fraud has become a significant concern for businesses across the UK and beyond. In fact, according to UK Finance ‘more than £500 million was stolen via APP fraud from businesses in 2022 alone.’

Sean Moriarty, CFO,
AccessPay
In our recent webinar How to Ward Off APP Fraud: Talking Enhanced Payment Controls with a CFO, we sat down with Sean Moriarty, the Chief Financial Officer of AccessPay, to discuss APP fraud, its prevalence, and the effective measures businesses can take to prevent it.
This blog delves into their conversation, highlighting the key takeaways and strategies discussed.Watch the full webinar on-demand
What is APP fraud?
Authorised push payment fraud refers to a sophisticated scheme in which a fraudster tricks a business into willingly sending funds to a fraudulent account. This deception often involves the fraudster masquerading as a genuine supplier, employee, or financial institution. One of the most concerning aspects of this type of fraud is that it operates under the guise of authenticity, relying on social engineering tactics and advanced technological tools to deceive unsuspecting victims, normally within the finance team.
Why is APP fraud so prevelant?
APP fraud has gained prominence due to a combination of factors. The financial rewards for fraudsters are enticing, as even a few successful attempts can lead to substantial gains for an individual. Moreover, the digital era has provided fraudsters with ample tools to execute their schemes, including the ability to hack into email accounts, create fake documents, and even mimic the communication styles of senior executives. As remote work and electronic communication has become the norm, the opportunities for fraudsters to exploit these vulnerabilities is only increasing too.
A real world example of APP fraud
During Sean’s career as CFO, he’s seen many examples of APP Fraud.
One of his fellow CFO contacts recently highlighted a shocking example where a corporate finance team was directly targeted, and suffered a substantial financial loss.
The Scenario: Uncovering an APP Fraud Scheme with Screen Sharing
- Company: Anonymous
- Initial Contact: Victim receives a call appearing to be from Barclays, reporting suspicious account activity and blocked outgoing payments.
- Request for Funds Transfer: The caller convinces the victim to transfer funds back to the company’s account from a holding account, creating urgency.
- Screen Sharing: The fraudster suggests a screen-sharing session to resolve the issue more efficiently, and the victim agrees.
- Manipulating the Screen: During the session, the fraudster gains control, displaying transactions that seemed genuine to the victim, but were manipulated.
- Authorization Code Request: The fraudster asks the victim to enter an authorisation code, concealing the actual transactions being approved.
- Unintended Transfer: The victim unwittingly authorises different transactions, resulting in a £200,000 loss for the business.
This incident serves as a stark reminder of the importance of implementing the right security checks to prevent such scams in the future, a lesson we will delve into further as we share examples of preventative measures.
3 ways you can combat APP Fraud
 Spotting the red flags and common tactics
Spotting the red flags and common tactics
There are several examples of APP fraud instances, ranging from sophisticated spear phishing attacks to direct manipulation of payment processes. These real-world scenarios underscore the importance of staying vigilant and implementing multi-layered defence mechanisms within organisations. Recognising the common tactics employed by fraudsters — such as creating a sense of urgency, exploiting personal details, and manipulating email communication — can empower finance teams to identify potential scams before they escalate.
In the case mentioned above, it’s evident the victim should have called the bank back on a direct number, but the urgency created by the fraudster was enough for the victim to feel pressure to resolve the issue, quickly.
It’s always best to speak directly with a more senior colleague if any communication or payment appears irregular. Here, the common tactic was to ‘panic’ the victim, and unfortnately in this case, it paid off.
Sean provides a real-life example of APP Fraud and how he overcame it.
 Building effective defence strategies
Building effective defence strategies
To combat APP fraud effectively, businesses need to adopt a comprehensive approach that encompasses both employee training and technological solutions. Establishing a strong collaboration between finance, security, IT, and governance, risk and compliance (GRC) teams is crucial.
Regular training sessions can enhance the ability of employees to identify and report suspicious activities. Additionally, the integration of technology, such as confirmation of payee services, can provide real-time checks on account details, ensuring that payments are directed to legitimate recipients.
Such training equips individuals and organisations with the knowledge to identify common fraud tactics, including phishing emails and manipulative communications. It emphasises the importance of verifying payment requests and recipient information, promoting practices like Confirmation of Payee (CoP) (more on this later) to prevent fraudulent transactions. Additionally, training instils secure digital habits, such as robust password management and vigilance against phishing attacks.
In corporate settings, specialised training enhances employee awareness, reducing the risk of insider threats. In the case Sean mentioned, as his staff had had the correct training they were prepared and ready to question phishing attempts of that nature, but of course there is situations where businesses aren’t so lucky. Facebook and Google have even fell victim to this; A Lithuanian man, Evaldas Rimasauskas orchestrated a classic case of business email compromise (BEC) in which he, along with co-conspirators, successfully stole over $100 million from Facebook and Google. They impersonated Taiwan-based Quanta Computer and sent convincing phishing emails containing forged invoices and contracts over two years from 2013 to 2015.
Want to know more about how to implement effective defence strategies?
Download our free guide: The Finance Leader’s Guide to Combatting Authorised Push Payment Fraud
 Leveraging technology for prevention
Leveraging technology for prevention
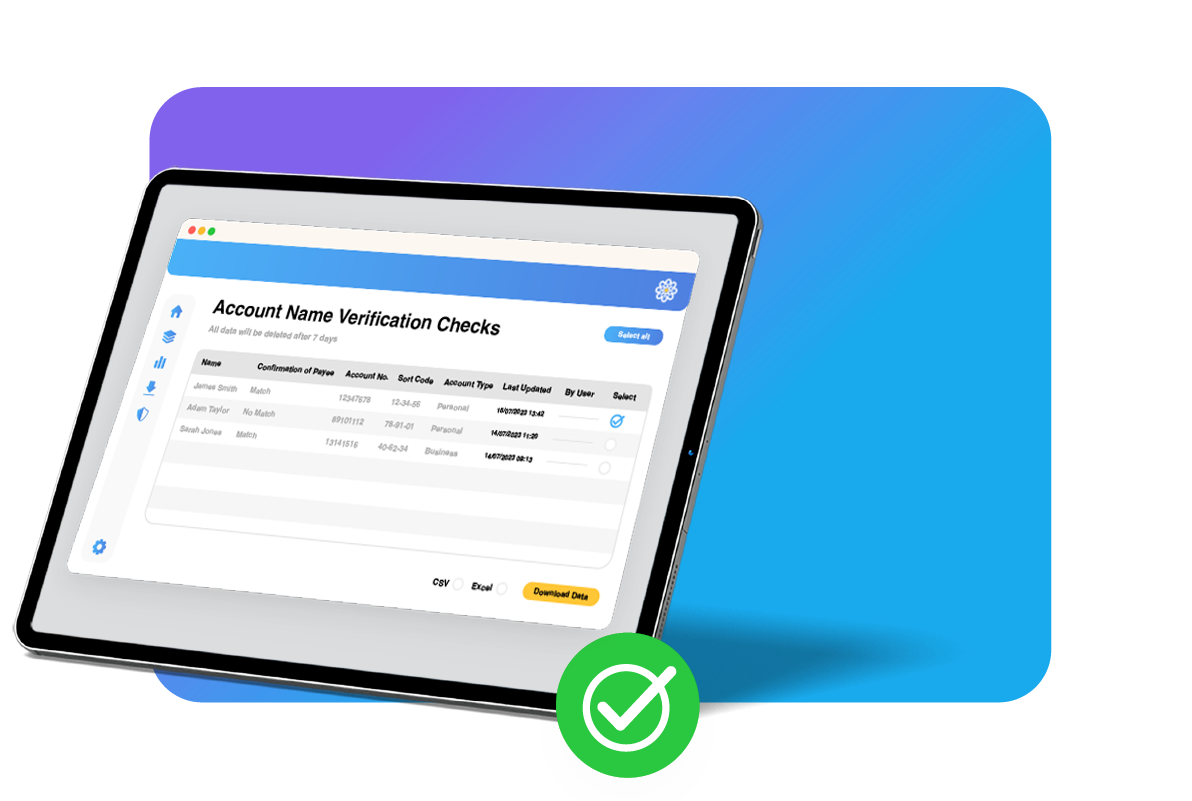
Account Name Verification (ANV) plays a pivotal role in thwarting APP fraud attempts. ANV allows organisations to cross-reference account numbers, sort codes, and account names to ensure they match.
By conducting these checks before initiating payment runs, businesses can identify inconsistencies and prevent funds from reaching fraudulent accounts; serving as a robust authentication layer. Any name mismatch triggers an alert, prompting the payer to verify the transaction. ANV thwarts social engineering tactics used by fraudsters and enhances traceability in case of a breach.
If this victim’s team had decided to make a payment, the ANV feature would have been crucial in protecting the organisation. It would have flagged the inconsistencies between the account name and the person being paid, stopping the payment from being authorised until these details were reviewed.
 More on how to implement and automate ANV within your financial processes here
More on how to implement and automate ANV within your financial processes here
APP fraud poses significant risks to businesses of all sizes and industries. However, with a proactive approach that combines employee education and technology-driven solutions, organisations can mitigate the risk of falling victim to these sophisticated schemes.
By maintaining a strong collaboration between finance and security teams and leveraging advanced tools like ANV, businesses can bolster their defences and protect their assets from the ever-present threat of fraud.
Find out more about Account Name Verification, and ways you can detect suspicious transactions before they are made, with our Fraud & Error Prevention Suite.
